Dado um regresso de medidas mais restritivas relativas a agregações de pessoas em Lisboa, adiámos o evento e vamos fazê-lo online
Notes from the Event:
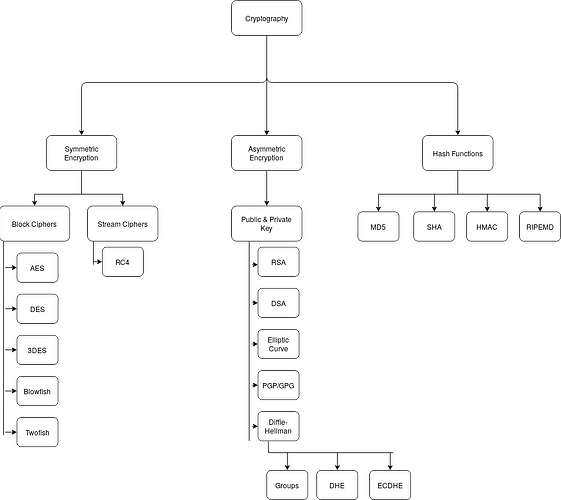
CRYPTOGRAPHY
What is it?
Cryptography or cryptology is the name given to the sum of various techniques that enable secure communication between the sender and the intended receiver.
Why do we need it?
Because humans have always had the need to be secure and private through out history whether they have been trying to keep their war strategy secret or they did not want mean people to steal their credit card information when they do online shopping.
What is the relation between Cryptocurrencies?
Cryptocurrencies use cryptology techniques to secure their platforms. Cryptography is not a monetary currency and existed long before cryptocurrencies. Cryptography is more about math and logic than money or economics.
Types of Cryptography:
Encryption
Encryption is used for confidentiality. Meaning data is only viewable by authorized user.
Encryption ciphers (scrambles) data to make it useless even if someone got their hands on to it.
Encryption requires random/pseudo-random numbers as an input. Easy? Not really. It is impossible to generate a true random number with a computer since computers don’t really do things “by chance”. But they can generate pseudo-random numbers by a deterministic algorithm/math magic.
An initialization vector (IV) provides a starting value for a cryptography algorithm. IV is a fixed size random or pseudo-random number that helps create random encryption keys.
A nonce is a number used once.
XOR is a logical operation that compares two inputs. If two inputs are the same, it outputs false (binary 0), else it outputs true (binary 1).
when ciphertext is significantly different than the plaintext, it is called confusion in the context of cryptography.
Diffusion ensures that small changes in the plaintext result in large changes in the ciphertext.
Symmetric Encryption
-
uses same key to encrypt & decrypt data (public key)
-
most use block cipher or stream cipher.
-
change keys much more often than once a day
What are ciphers?
-
They are also known as cyphers
-
A cipher is an algorithm to perform encryption
Block Cipher
-
encrypts data in specific-sized blocks
-
Such as 64-bit blocks or 128-bit blocks.
-
It divides large data into these blocks and then encrypts them
-
More efficient when size of the data is known such as when encrypting a file.
Different Modes for Block Chippers:
Electronic Codebook (ECB): encrypts each block using the same key. Not safe, deprecated!
Cipher Block Chaining (CBC): uses IV for randomization for the first block. Then uses XOR operation to encrypt rest of the blocks. Meaning each block is dependent on the previous block before it. Dude to this dependency, CBC can suffer from pipeline delays. Making it not super efficient.
Counter Mode (CTM): converts block chipers to stream chipers. Uses IV with a counter. Each block has the same IV value combined with a counter meaning each block ends up with different keys at the end. Especially efficient in multicore and multiprocessor systems. Respected and widely used.
Galois/Counter Mode (GCM): combines CTM with data authentication method. Encrypts and Hashes meaning provides confidentiality and integrity. Widely used due to efficiency and performance.
Block Ciphers:
AES Cipher
Advanced Encryption Standard
encrypts data in 128-bit blocks
can also come in 192 bits or 256 bits
it is fast, efficient and strong
Still in use and recommended by NSA
DES Cipher
Data Encryption Standard
Outdated, was hot back in 70s.
Now it is a piece of cake to brute force it
3DES Cipher
Came as an update to DES
uses key sizes of 56, 112, 168 bits
encrypts data in 64-bit blocks like DES does
basically does the same math DES does but 3 times ![]()
not as often used as AES since AES is less resource intensive
bit if hardware is not suitable for AES, then you can go for 3DES
Blowfish Cipher
encrypts data in 64-bit blocks
supports key sizes between 32 and 448 bits.
Some sources claim Blowfish is prone to birthday attacks
Twofish Cipher:
encrypts data in 128 bit blocks
supports key sizes: 128, 192, 256 bit.
Stream Cipher
-
encrypts data as stream of bits or bytes rather than dividing it into blocks.
-
More efficient of the size of data is unknown or sent in continues stream such as when streaming audio or video.
Stream Ciphers:
RC4 Ciper
can use between 40 and 2,048 bits
for many years it was used for SSL and WEP
Now not recommended.
Asymetric Encryption
-
uses two keys (public & private)
-
anything encrypted with the public key can only be decrypted with the matching private key.
-
private keys are never shared
-
public keys are freely shared by embedding them in a shared certificate
-
very resource intensive
-
mostly only used to share symmetric keys between parties. Then switch back to symmetric encryption.
RSA
(Rivest, Shamir, Adleman)
it is an asymmetric encryption method
used extensively for web site encryption
a key size of 2,048 is recommended till 2030
a key size of 3,072 bits is recommended after 2030
Elliptic Curve Cryptography (ECC)
-takes it easy on processing power
-suitable for small wirless devices
Diffe-Hellman (DH)
is a key exchange algortihm
supports both static and ephemeral keys
DH by itself doesn’t encrypt or authenticate
DHE: Diffe-Hellman Ephemeral uses ephemeral keys, generating different keys for each session.
ECDH: Elliptic Curve Diffie-Hellman DH combined with elliptic curve cryptography
Groups: there currently are more than 25 DH groups. Higher group numbers indicate the group is more secure.
PGP/GPG
Pretty Good Privacy (PGP) used to encrypt and digitally sign emails
OpenPGP is basically open source PGP, free of licensing fees
GNU Privacy Guard (GPG) is free software based on OpenPGP
All PGP versions use RSA
Hashing
-
Hashing is an algorithm performed on data
-
Hashing creates fixed size string of bits or hexadecimals
-
Hashes are commonly shown in hexadecimal (0-9 & a-f) format instead of bits (1’s and 0’s)
-
You can verify integrity with hashing, meaning you can make sure the data has not been changed.
-
Hashing is a one way road with no turning back (You technically can turn back but it is not feasible given how much computing power it will require)
Hashing in Examples
Hashing is widely used for saved passwords. When we create a new password, the hash of the password is calculated and saved instead of the actual password we created. Afterwards, each time we sign in to our accounts, the hash of the password we enter is compared with the hash that was originally saved. Since hashes of same data is identical, if the systems stored has does not match with the hash of the one we entered, the system refuses out access and vice versa.
Hashing Algorithms:
MD5
-
Message Digest5
-
Produces 128-bit hash /displays 32 hexadecimal characters
-
Has been in use since 1992
-
Vulnerabilities found starting from 2004
-
Processing power of computers increased, became easy to crack MD5.
-
So you better don’t use it!
SHA
- Secure Hash Algorithm
Several of them exists:
SHA-0: replaced by SHA-1 shortly after it was created. not secure.
SHA-1: similar to MD5 but creates 160 bit. Not secure. (created by NSA)
SHA-2: it included 4 versions, each with different bit. (created by NSA)
SHA-3: can create hashes of the same size as SHA-2 (was selected at a non-NSA public competition)
HMAC
-
Hash-based Message Authentication Code
-
fixed length string of bits like MD5 and SHA1
-
Also uses a shared secret key to add randomness to the result.
-
Only sender and receiver know the secret key
-
It pretty much builds on top of either MD5 or SHA1.
-
Hashes with either algorithms and then adds the secret key for randomness
-
With the secret key, not only it checks integrity, it also checks authenticity
-
IPsec and TLS often uses a version of HMAC
-
very useful for exchanging messages such as emails
-
It is possible for an intruder to change not only the message but also the hash of the message and fool the receiver that the integrity of the message is still intact
-
With HMAC and secret key, because the intrudes is not aware of the secret key, s/he also cannot change the hash. Meaning the receiving party will recognize that the integrity of the message has been lost.
RIPEMD
-
RACE Integrity Primitives Evaluation Message Digest
-
Not widely used
-
Has different versions with bit sizes: 128, 160, 256, 320
Is Hashing by itself enough?
When used the same hashing algorithm, the hash will always be the same if the data is the same. This is a major security problem hence the reason why we use salt and pepper.
Salting the hash means adding random values to it. It can also be known as **key stretching. **
We can also pepper which is a secret added input to the password and unlike salt, it is not stored with the password. Instead it is stored separately.
Two key stretching techniques are Bcrypt and PBKDF2
Bcrypt:
-
based on Blowfish block cipher
-
used on many Unix and Linux distros
-
Bcrypt adds salt and pepper if needed before encrypting data with Blowfish
-
resulting has size is 60-character string
PBKDF2
-
uses HMAC for encryption
-
uses salt of at least 64 bits
-
resulting hash sizes can be: 128 bits, 256 bits, 512 bits
-
iOS and Cisco uses it even though it now is getting old and newer key stretching techniques such as Argon2 is proven to be more secure.
Obfuscation
XOR:
Exclusive Or.
Outputs true when inputs differ (binary 1)
One time pad offers perfect security, but is pretty unusable in practice.
Substitution Cipher:
replaces plaintext with ciphertext with a fixed system. For example moving letter 3 times. “Pass” turns into “Sdvv”
Considered insecure.
ROT13:
is also a substitution chipher that is fixed to number 13. Letters would move 13 spaces. This is not really a true encryption since the key is fixated to 13. it is more of an obfuscation.
Obviously considered insecure.