💡Ideas Box 📦
Take one, leave one
If you like one in particular that you would like to discuss, copy it into a new topic and let’s start discussing
These are just some ideas for privacy workshops/talks that might be interesting to cover.
They just sit here until someone decides to pick it up. Feel free to share, remix however you like and contribute back if you have something interesting in mind. You can do that as a pull request or if you don’t have a github account, e-mail one of the organizers at francisco.core.at.protonmail.com.
When the idea is getting bigger than a small description, you can create a new directory like “Topics/name-of-your-idea” and expand it as much as you would like in there, add images, presentations, etc. And then add a link from this document to your other one.
Feel free to use any of these ideas on workshops of yours !
Censorship Simulation
event format: exhibition
Create a censored environment with various levels of censorship:
- DNS censorship - people will have to change the DNS
- IP Blocking - use tor or some sort of VPN
- Tor is Blocked - people will have to use bridges
- Deep Packet Inspection - obsfproxy
The idea is for people in understand that there are various types of censorship and know how to get around them. It would also be valuable to explain what kinds of censorship are in use in particular countries.
There is a scientific article that talks particularly about this: McGregor, S.E. et al. Investigating the Computer Security Practices
and Needs of Journalists
Censorship on Europe
event format: talk
Explain to people the kinds of censorship.
Camera recognition
event format: exhibition
The idea here would be to use facial recongition algorithms and instread of training them on faces, train them on CCTV cameras of all types. Creatively subvert the objective of these technologies while also creating awareness about surveillance.
Note: Probably someone has already made this. Is you are aware, feel free to post a link
Android Forensics Study Group
event format: working session
How to tell if malware/surveillance software has been added to a cell phone?
How to tell if data has been extracted from a phone?
These are questions which have been explored in the AnarchoTechNYC. Take a look there
Digital Fight Training
event format: workshop
These are digital privacy and security workshops, but from a bit more technical and offensive side.
Take a look at the wiki entry from AnarchoTechNYC.
Facebook Rehabilitation Group
event format: discussion
Facebook is made to be addictive and the fear of missing out is a huge psychological effect that keeps people locked into the platform. We should enable a discussion where people talk about the issues that keep them locked on the platoform and what can be done to help them leave it.
note: do the same with google
Investigating Metadata collection by the PT Govt
event format: working session
The european union passed a law that was considered later considered to be against the fundamental rights of the citizen. The law find source mandated that telecom provides recorded metadata for two years. But since it was a directive, it was implemented in every country’s laws and when it was conidered illegal, it was already too late. Now the law has to be abolished in every single EU country’s tribunals. In Portugal the law was apparently considered inconstitutional. But then it seems that a loophole allowed for the continuation of that collection and use. We should investigate a bit more on this.
note: supposedly this is no longer in the law thanks to our friends at D3 who brough the issue to the constitutional court.
What data companies have on me? - a dive into data exportability
event format: workshop
In europe, with the GDPR, (an possibly in other places - due to the brussels effect) people have the right to ask for the data stored about them such that they can move to another service. Some services
had already allowed people to take their information, but other only how implemented it. The idea is
to show people what kind of data they have uploaded onto these platform.
Here are some links to export data:
- Amazon
- Alexa Recordings
- Apple
- Facebook (off-site activity)
- Snapchat
- Tinder
- Twitter
Links were originally compiled by Michael Bazzel in his podcast Intel Techniques
Two other project that might help with this workshop:
- https://personaldata.io/ - they catalog the types of data that these companies store on you and automate making these data access request. Find their forum here
- GDPRHub - a project of cataloging info about the GDPR (organized by NYOB)
- Your Data Done Right - a project by Bits of Freedom to help you make data access requests
Demystifying Encryption 

event format: workshop
For many people encryption is a buzz word for security and it is some sort of magic bullet that solves everything. In reality there are different kinds of encryption and it important for us to know how to differentiate the. Even more than that, it is important to ask the right questions about that technology. Questions such as:
- Who has access to the data
- Who controls the keys
- Is it open and well documented?
- Is the technology standardized?
Note: Talk about Metadata too in this event
Exploing what metadata is.
Introduction to steganography
event format: workshop
https://incoherency.co.uk/blog/stories/image-steganography.html
https://incoherency.co.uk/blog/stories/chess-steg.html
Playing with algorithms
event format: workshop
Create a new identity on the web and try to reach a certain profile. Example: female, likes makeup, or male that gets adds about watches, etc. And see the adds for that
do the same with amazon and facebook.
some work has already been done in facebook.tracking.exposed
we need to talk about China…
event format: talk
China is evolving in a fast pace to becoming the first digital dictatorship.
We should do a presentation.
*Facial recognition to take college attendance
- Attendance face recognition Access control
- Mobile Attendance App with Face Recognition
Face Recognition system using in students Identification
Digital Mirror
event format: workshop
Make people see what advertising companies think they are and compare with other people. Use a script that takes pictures of the adds shown to each of us and compare them. Maybe some will not even like that they are shared because they are so personal. And it is an opportunity to show people how much information these companies have on you.
the digital dopleganger that those companies have of us
QubesOS meetup
event format: workshop/gathering
QuebesOS is an awesome Operating System and it deserves to have people chat about it. So let’s share your experiences with it and introduce new people to the concept of compartmentalization at the operationg system level.
Breaking Windows Tea Party
event format: workshop
Let’s break away from Windows. Let’s install software that promotes freedom and gives us power instead. In this workshop, we shall guide people on the adventure of venturing to a new operating system. There will be chanllenges ahead, but the destination is a much better place and well worth the turbulent trip. So let’s sail to that island together and help eachother with our difficulties.
Monthly Privacy Cafe / Cryptoparty / SecurityTea (SecuriTea?)
event format: workshop
Basic Idea: gather people around the topics of surveillance and privacy on an informal encounter.
Cryptoparties are the original idea
Privacy Cafes are an idea from Bits Of Freedom and they have some material here - all in NL ![]()
SecuriTea is the same but from the cypurr collective
This social event from the CyPurr Collective hopes to provide a comfortable space to discuss these anxieties as well as current events in the digital world. Let’s build up our digital-agency and form a critical understand the tech encroaching on our lives. All while enjoying delicious tea and snacks, of course. https://cypurr.nyc
Wifi Tracking
Do you see those “free” wifi hotspots everywhere and sometimes there is more than one (to give you better internet) ? Well, they also see you. A possible idea for a talk/workshop would be talking about these devices and give concrete examples. Maybe do a road tour and play around with these device.
This guide here is a great introduction to the topic.
More examples:
- In a university in Lisbon they are using wifi to track students (to save energy costs, they say)
Electricity Smart Meters
Electricity smart meters are being installed all around us. They tell all about what is going on in our house:
- When we are there,
- When whe are not
- When we have vistors
- When we are having a party
- When it looks like we are running a business from our homes
That information can and will be abused:
- It will be used in court as possible alibi or testemony (against you)
- Will raise questions on what you are doing on in your house
- Will be used to determine if you are at home. Just imagine someone knowing whether or not you are at home just sitting on a desk.
- They can use that to gamify your life. Give you bonus points if you have certain habits
Here is a video about it and here (Portuguese) a discussion thread on the topic.
These work like wiretapping devices
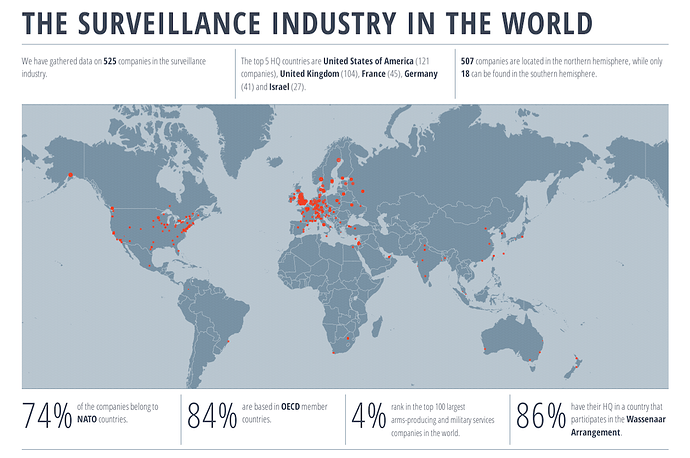
Investigating Surveillance
event format: working session
It has been some years now, but the Snowden documents still contain relevant information. We should do a working session where we analyze the these documents, and more recent leaks.
We can also look at the catalogues of surveillance companies to see the kinds of capabilities they advertise. To help in this, privacy international’s surveillance industry index might be of help
During the working session we could search and anontate documents with the helo of UWAZI. It’s a took for human rights researchers that makes investigations with documents much easier.
Useful material:
- snowden archive from cjfe https://www.cjfe.org/snowden and here https://snowdenarchive.cjfe.org
- other snowden archive https://search.edwardsnowden.com/, which was produced by transparency toolkit. Source data here.
- privacy international’s surveillance industry index
Investigating Large Databases
event format: working session
We know that in europe as well as around the world there are huge dataset from people all around the world. We should do a working session to find what these are at leas so we have some notion of what is going on.
Tracking the Trackers
event format: working session
Taking a look at the marketing industry, look for catalogs and the stuff they sell. Because their websites look like they went straight out of Brave New World.
HomeApp Centre | Me and my Shadow (find the videos on databrokers, metadata)
Documenting COVID-19 surveillance
event format: working session
Containment measures imposed during the COVID-19 outbreak in 2020 are really great excuses to surveil everyone. We’ve seen countries surveilling everyone’s phone location but fore sure many other measures are being implemented it’s just that we haven’t cataloged them.
During this session the people present will help aggregate in a document the various kinds of surveillance practices that have been introduced under the guise of contaiment measures, in an effort to find the big picture of how much our privacy has been impacted. And perhaps it the end result has enough quality it can even be posted as a blog/forum post.
Documentary Session
event format: film projection
Citizenfour, article12, Nothing to Hide, Information: what are they looking at, etc.
Is the notion of privacy culture-dependant?
event format: workshop
Get some inspiration here Youtube | Yao Li - Cross-cultural Privacy Prediction
New Privacy Threats
event format: workshop
-
Gigapixel
There are these cameras that sit on top of a building and take a picture with millions of pixel. This means that we will lever see the camera, but it will see us from very far way.Examples:
Tracking Ourselves and Each-other
event format: talk
Peer-surveillance is when someone surveils or tracks others within the same circles. Think of parents tracking their children (look for US patent 2016/0183693 A1 Google), people tracking their health data, foursquare.
Understanding the Surveillance by Looking at Patents
event format: talk/working session
- US patent 2016/0183693 A1 Google
- Facebook patent on tacking people on supermarkets
- Look for facebook’s other companies
Maybe do a presentation on the most distopian patents. Maybe do a contest of the patents in a workshop where we choose the worst one (big-brother award-like)
Some examples:
| Patent | Company | News | Patent Application | Pattent code |
|---|---|---|---|---|
| Tacking people through camera dust | gizmodo | here | US20160014677A1 | |
| Wireless communications to suggest connections for a user | - | here | US20160014677A1 | |
| Find people’s real friends even if they don’t use fb much | - | here | US20160014677A1 | |
| Trigger Phone’s Mic When a Hidden Signal Plays on TV | [gizmodo](news article) | here | US20180167677A1 | |
| Google spying teddy bear | cnn | here | US20151038333A1 | |
| Correlating media consumption data with user profiles | nytimes | here | US20170195435A1 |
Where to find more patents:
Google Search Manipulation
event format: workshop
Show people how google manipulates search results and use that to motivate questioning on the social impact of google. Prove alternatives to the people so they have a choice
Google tracks us even in airplane mode
event format: workshop
Do a workshop where we MITM to test this ourselves https://www.youtube.com/watch?v=wd_lhqi2NcA
2FA Workshop
event format: workshop
software tokens / sms can be compromised (MITM)
Harware devices are better
Mobile phones insecurity
event format: workshop/talk
Phones are very old technology and with old stuff comes insecurity. Simply because that was not a concert at its inception. Meanwhile, we keep using them, but that fragility can use used against use. We could explore some topics on this insecurity.
IMSI Catchers
event format: workshop
As documented here: GitHub - Oros42/IMSI-catcher: This program show you IMSI numbers of cellphones around you. and here
Here's How Easy It Is to Make Your Own IMSI-Catcher
to understand the capabilities of such devices and doing so in a controled environment to make sure that no-one’s privacy is violated and within the limits of the law.
Location Tracking by communication operators
event format: talk
But who needs imsi catchers if the communication operators can know what people are talking as well as phone’s locations at all times. This motherboard article explores how in the us that data is broadly missused.
In many EU countries there is a metadata law that requires telecom companies to store location data of phones via the tower they connect to for two years. This means that they know where you have been every single day for that time period!
Creating good passwords
event format: talk
Teach people how to use passsword managers
A workshop was made on this topics. We will publish the resourced produced shortly
Compartmentalization
event format: talk
Compartmentalizaton is a security principle for not having everything in the same place. Some of you might know the expession “not putting all eggs in the same basket”. That’s what this presentation is about.
Practical measures like using “firefox multi-account containers”, creating accounts in different services or using fake accounts are covered.
A presentation by privacylx was made on this topic and the slides are avaiable on github.
Insecurity Demonstrations Mini-Hackathons
event format: workshop/hackathon
One typical problem with explaining to people how deep the privacy violations go is because in tech, everything is kind of invisible. The purpose of these sessions is for us to collaborate on tools that help people visualize what is going on in the background.
Ideas for project:
- Simple IMSI catcher: GitHub - Oros42/IMSI-catcher: This program show you IMSI numbers of cellphones around you.
- Pirogue MITM: GitHub - Oros42/IMSI-catcher: This program show you IMSI numbers of cellphones around you.
- Censorship Simulation: explained above
- Hack amzon echo to spy on people
- javascript-less tracking demo: see more in Cursor tracking without Javascript
Talking about IoT
event format: talk
inspired on ccc event
does it really need to be online
Island of Things is better than an internet of thinks
Disrupting IoT examples:
- project that blocks voice recordings by personal assistants [news article]
Some links related to Iot invading people’s privacy:
Privacy, Creativity and the Chilling Effects
event format: talk
This could be a talk of a discussion. Maybe with some slides before talking about surveillance.
Surveillance poisons the discourse.
this whould also have some practical examples. Amnesty International has some great study cases on Belarus and how surveillance might have affected protests or lack-thereof.
Stasi knew about this. Maybe we should also cover this.
Also talk about how this affect and individual’s creativity. It might be important to talk about the social cooling
Introduction to Email encryption
event format: workshop
Protonmail and other modern email webapps has a nice interface for doing email encryption. We could teach people through there or maybe also do it through thunderbird.
WARNING: Warn people that protonmail may reveal a person’s language if they use iOS, for example. The replied message contains the translated string of “from” and the date.
Onion Services Introduction
event format: workshop
On this workshop we would be creating an onion service - a way to host a website without exposing your server location and making sure people accessing it use tor.
There are other advantages that can be covered too:
- very easy to setup
- no DNS / authentication is in the url
- nat punching
- non-enumerable
- making sure people use tor to access it
- authenticated onion services to do access controll
security considerations: check out riseup’s wiki
Should we be using chrome?
event format: workshop/working session
Explore together with others how privacy invasive chrome really is. The base for this session would the chrome privacy whitepaper, which is a document that details all the surveillance that chrome does (they must call it a “privacy paper” ironically).
At the end of 2018, google (the company that develops chrome) silently pushed an update that automatically login in to chrome any user who had logged into a google account without consent or notification. We aready knew that having a company like google as owner of the browser we use could be a bad idea. I guess we just needed proof that it could lead to more privacy invasions.
But many more privacy invasions happen in chrome and we’re not even aware of them. This will serve as an eye opener to what google really is seeking - our souls ![]()
Cooperate With Artists to create Awareness
event format: ?
Invite artists to brainstorm on ideas to raise awareness on privacy issues and also inform them.
Using Facebook to get people out of there
event format: online activity
- link out and not in. Send people links to your website and keep it updated instead of sending people to your facebook
- create facebook suicide parties / use sth like http://suicidemachine.org/
How to delete facebook
event format: workshop
Teach people how to safely backup a facebook account. Maybe pollute it a bit before leaving in order to confuse the algorithms.
Facebook’s Censorship
event format: talk
We know facebok is bad for a lot of reasons and it is worrisome why so many people are still there. In this proposal for a talk we would expose facebook’s actions and make people rethink their positions. Examples
-
We can no longer talk about sex on Facebook in Europe
Sometime in late 2018, Facebook quietly added “Sexual Solicitation” to
its list of “Objectionable Content”. Without notifying its users. This
is quite remarkable, to put it mildly, as for many people sex is far
from being a negligible part of life.on edrigram 17.1 16th jan 2019
And maybe find other examples.
CryptoBar
event format: bar
Show people that there is no single strategy to be secure.
When you make a cocktail there is not a single recepy that is good. Infomrations security is pretty much the same
Note: maybe we can integrate this with cryptoparties and have a bar give us the space
What do they know? vs. What should they know
event format: workshop activity
Lineage Install party
event format: workshop
(or maybe call it “Degooglifying your android” / “owning the phone you payed for”). This might take some time and requires some preparation:
-
Prepare material to inform people of what will be needed
- phone
- backup done
- charger
-
Downloading images for the devices as the Internet at the venue might be too slow to do everyone’s download
-
Prepare a debricking guide to follow in case something goes wrong
Privacy Underground
event format: workshop/game
Privacy “Underground” - Computerphile describes a nice concept where people meet in a secret location revealed only on the day of the event and when reaching it, they need to turn off their smartphone.
A similar concept seems to be “Secret Dining”. With that idea, we could organize a diner where the main topic would be privacy and where the location is “secret”.
There could be a gamification aspect where we would disclose the location in an “encrypted manner” and only those who would decipher the message would be able to reach the destination. And maybe that could be like a short treasure hunt (30mins) to reach the dining place. That might create a good climate within the group as people all feel accomplished and that can be used to kick-start the dinner.
Exhibition: Another way of seeing tech
event format: exhibition
Have a display of everyday tech but labeled differently (more creepy but still true). The idea is to show everyday objects from another perspective.
| Name | alternative name | alt descritpion |
|---|---|---|
| smartphone | tracking device | a computer that is but on your pocket or purse buy which tracks your every move and sends to the cloud for “improving your experience” (sell the hell out of your data’s soul) |
| alexa | Telescreen | A device that people willingly put on their homes so their private conversation’s recordings |
| TODO | add more… |
Game: avoid google while browsing
event format: educational game
Have a browser open for people to try to navigate the web. When anything from google is loaded it play a “Doh!” sound. People will be amazed at how hard it is to win the game.
To make this more interesting for the player we may set an objective like “search for this festival” or “search for something you’re interested in”.
The first challenge is going to be interesting, actually. If people don’t know other search engines, how are they gonna find another search engine without a search engine.
educational objective: show people that google is not just there when they search on google. It’s everywhere! (75% of websites has some sort of google tracker).
Apendix: Event types
| Event format | Description | Room arangement |
|---|---|---|
| Talk | Some people talk to the rest of the group | forward-facing chairs |
| Workshop | There is some material prepared for people to follow and learn | various groups in tables |
| Working session | people in groups collaborate to investigate/work on something | various groups in tables |
| Screening | showing some piece of media, be it a film or talks | forward-facing chairs |
| Discussion | Everyone is invited to contribute to the discourse. | chairs in a circle |
| Educational Game | Something that we may have in other events | |
| Exhibition | Like a museum room |