What I keep hearing these days is:
“We/I do not use Zoom for confidential conversations.”
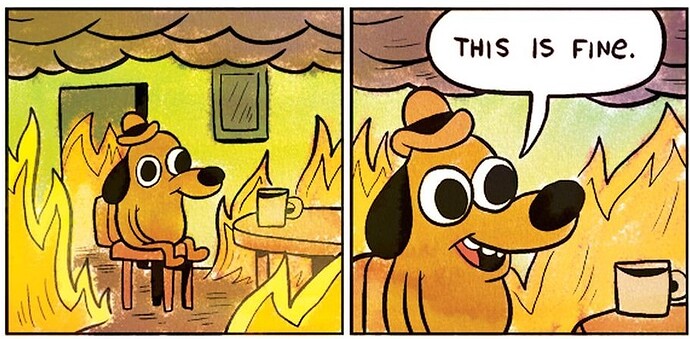
This is fine.But what if someone does not only care about the confidentiality of a Zoom-session but also about the integrity of his or her own endpoint device? It’s not only the spoken word of a group within a Zoom session that is at stake it is also the integrity and confidentiality of everything a conference participant has stored on their computer.
https://dev.io/posts/zoomzoo/
I think the cartoon they put there pretty much sums it all up. I still can’t figure out why the nothing to hide argument is so prevalent…
1 Like
And I guess this is related to your other post